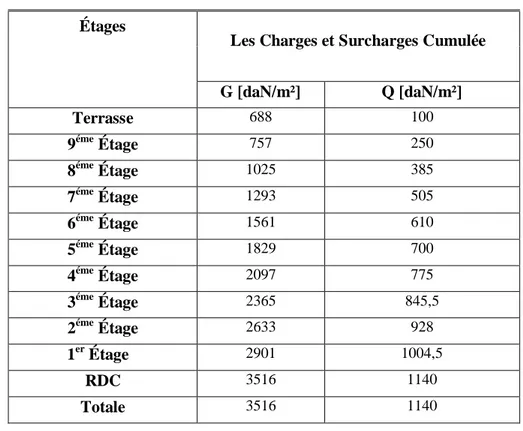
Etude d’un bâtiment (R+9 à usage d’habitation + Sous-sol)
Texte intégral
Figure



Documents relatifs
The last component of the state, the moved list τ , is used to accumulate the sequence of elementary moves that the imperative algorithm emits using the printf function.. Moves
In the case of graing onto TiN in the presence of iron powder, in combination with the thickness of aminophenylene layers previously graed on polymeric ion exchange membrane
لولأا بلطملا : ا ةكرش سيسأت نوناقلا يف راخدلال ينلعلا ءوجللاب ةمهاسمل يرئازجلا : سيسأتل مههجوت دنع ةمهاسملا تاكرش يسسؤم يلع يرئازجلا عرشملا ضرفي
To validate that increased DNA damage and cellular senes- cence in MiTF-silenced melanoma cells relied directly on the downregulation of the FANC pathway, we carried out
At the link layer, the security should be used for all types of frames. Each unsecured frame is a flaw that can be used by an attacker. The answer will depend on the
In ( Kimotho et al. 2014 ), the authors estimate the RUL by modeling and tracking the voltage degradation trend using a Particle Filtering (PF) framework. They introduced a
Both numerical and experimental validation of the PTD model is carried out in various practical NDT configurations, such as pulse echo and Time of Flight Diffraction (TOFD),
diminished the interaction of RXR/RAR with N-CoR NID through CoRNR1 (Fig. The analysis of the SAXS data using explicit models indicated that the 484.. decrease of