Localized Broadcast Incremental Power Protocol for Wireless Ad Hoc Networks
Texte intégral
Figure
Documents relatifs
Dans ce chapitre, nous proposons SR3 (Secure and Resilient Reputation-based Routing), un algorithme de routage s´ecuris´e et r´esilient pour le routage convergeant (tous-vers- un)
We have proposed a very flexible solution able to detect several kinds of attacks such as Fixed Clock, Random Clock, Misused Identity… The only countermeasure presented
As in previous chapters, measuring the quality of a given parameter configuration (i.e., a tentative solution to the problem) is a complex task that must evaluate the solution in
Fig. 2 gives an example for illustrating effective neighbor selection. Assume that a source vehicle A within the dotted circle receives a data packet from its left vehicles
Figure 1 plots the average finish time F h as a function of the number of hops h to the seed for both small and large size of pieces.. Each point in this figure is an average
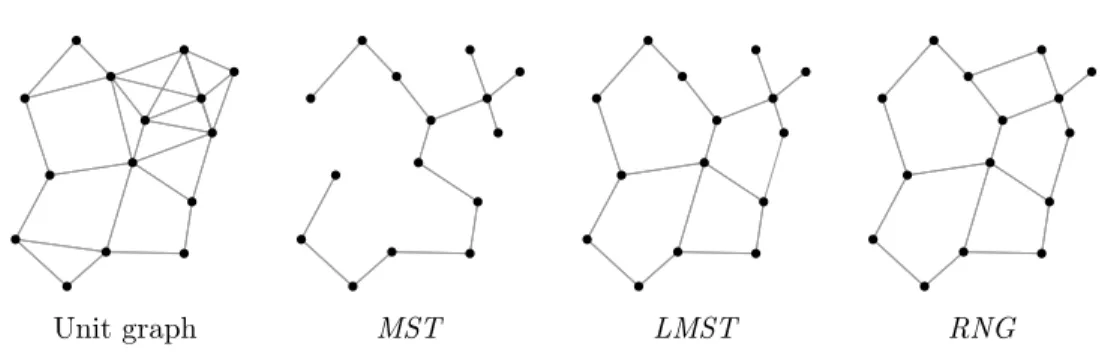
It is now commonly accepted that the unit disk graph used to model the physical layer in wireless networks does not reflect real radio transmissions, and that the lognormal
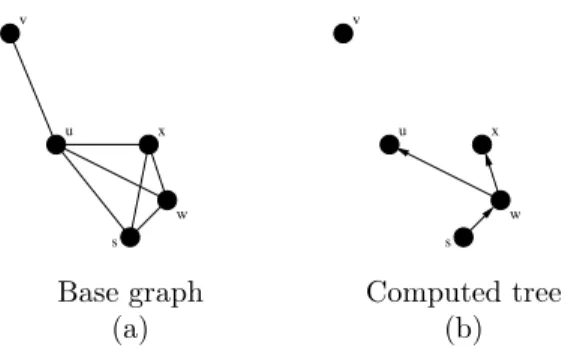
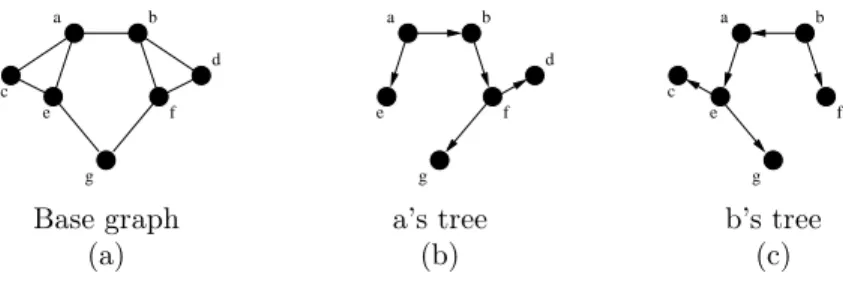
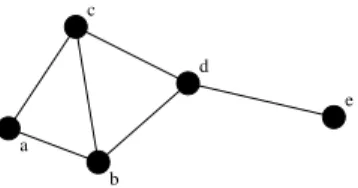
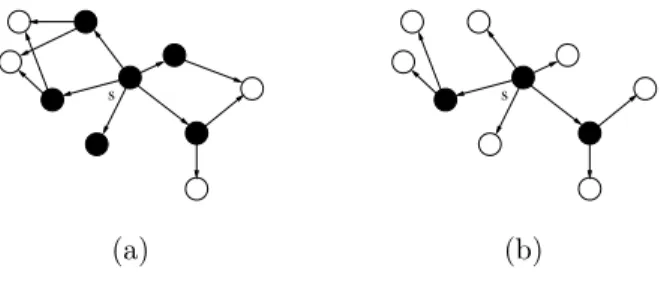
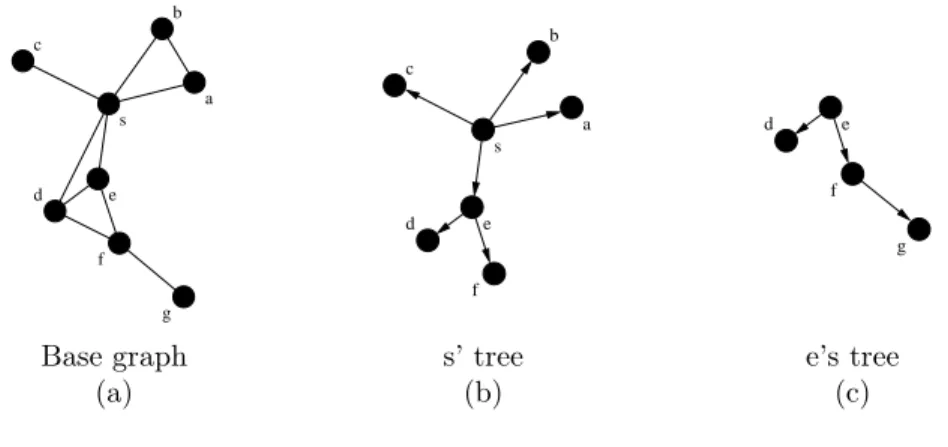
The algorithm can be described as follows: the source node s (which initiates the broadcasting) computes the BIP tree within its 2 -hop neighborhood, to determine which nodes
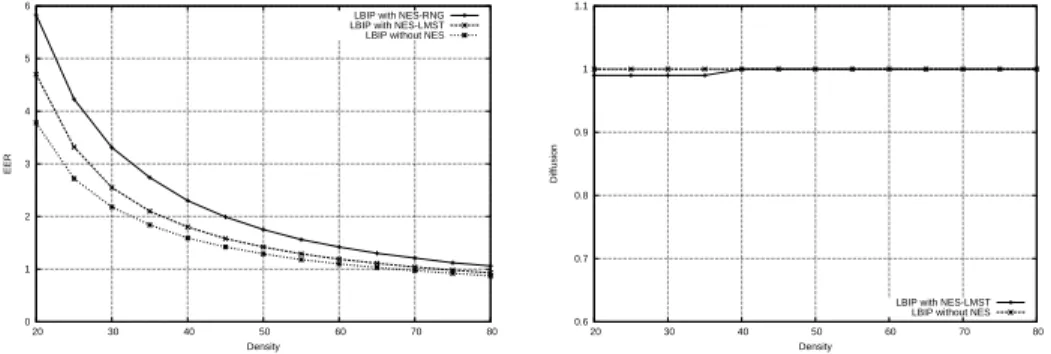
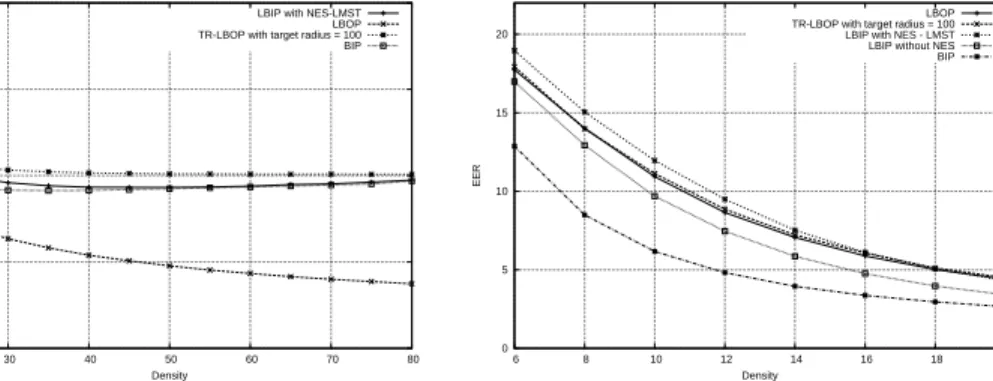
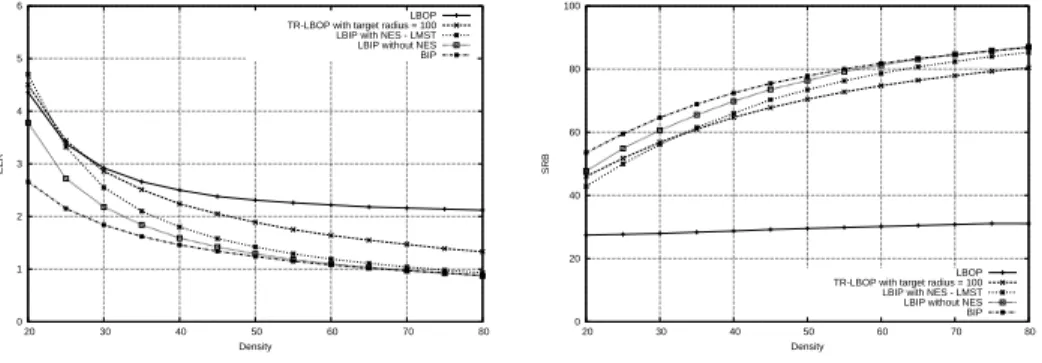
When a target radius of 0 is used, the nodes choose an average radius near to 50, which seems to be the minimal range needed for connectivity with the LMST in a network with density