A Model-based Repository of Security and Dependability Patterns for Trusted RCES
Texte intégral
Figure


Documents relatifs
/ La version de cette publication peut être l’une des suivantes : la version prépublication de l’auteur, la version acceptée du manuscrit ou la version de l’éditeur. Access
Mahloojifar, “A low-complexity adaptive beamformer for ultrasound imaging using structured covariance matrix,” IEEE Transactions on Ultrasonics, Ferroelectrics, and Frequency Control
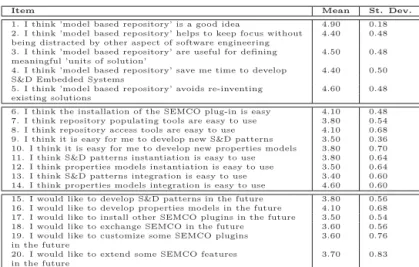
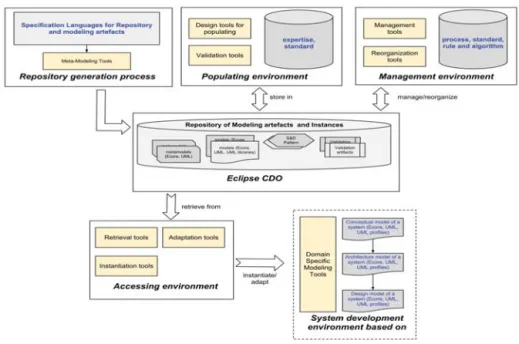
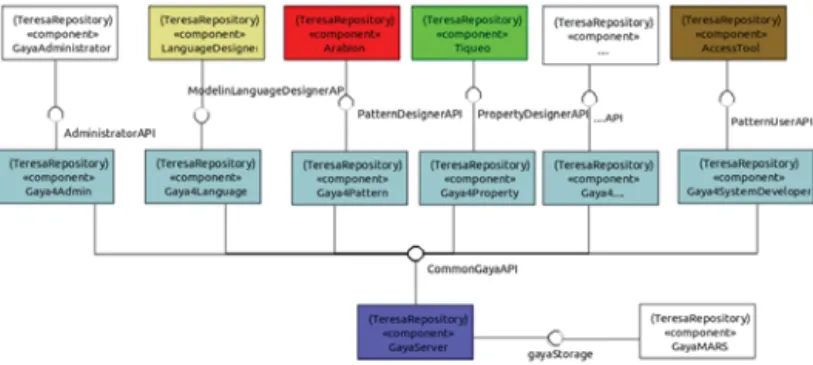
The contribution of this work is twofold: 1 An improvement of our previous pattern modeling language for representing security pattern in the form of a subsystem providing
In this work, we present a framework for trusted Resource Constrained Embedded Systems (RCES) development by design, by defining both a model to represent S&D pattern language and
We have verified that the sequential composition of the key management pro- tocols PKMv2 RSA, PKMv2 SA-TEK, and PKMv2 Key satisfies strong au- thentication and session secrecy for
They are collected, specified as reusable aspect models (RAM) [7] to form a coherent system of them. While not only specifying security patterns at the abstract level like in
The localized enrichment of Skittles and Pten acts to increase PI(4,5)P 2 levels at the anaphase equator, further promoting Moe recruitment at the equator and release at the
Aphanomyces euteiches cell wall fractions containing novel glucan-chitosaccharides induce defense genes and nuclear calcium oscillations in the plant host Medicago truncatula...