Is the fish-hook effect in hydrocyclones a real phenomenon?
Texte intégral
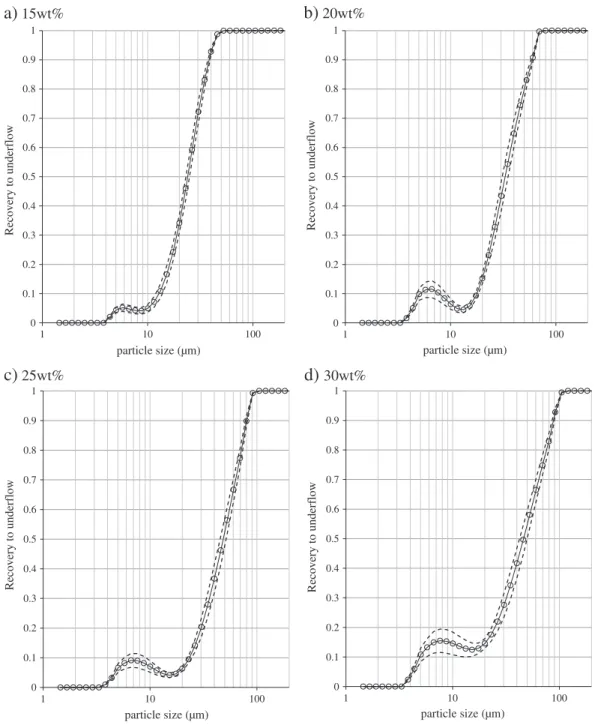
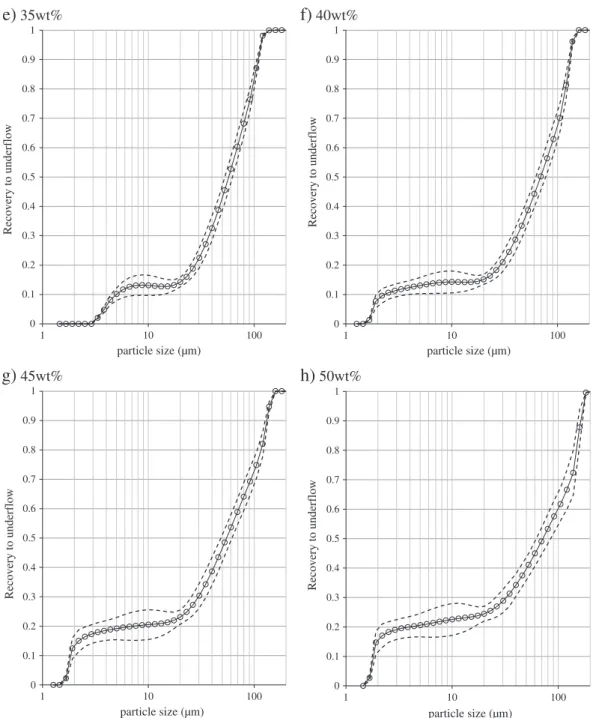
Figure



Documents relatifs
Although ISO 2022 specifies special additional escape sequences to indicate the use of revised character sets, it is suggested here not to make use of this special escape
While the IPv6 protocols are well-known for years, not every host uses IPv6 (at least in March 2009), and most network users are not aware of what IPv6 is or are even afraid
However, some types of trust anchor constraints may have defined additional steps, for example, CMS Content Constraints or Authority Clearance
If the FA allows GRE encapsulation, and either the MN requested GRE encapsulation or local policy dictates using GRE encapsulation for the session, and the ’D’ bit is not
In particular, bundles including the optional metadata block would be protected in their entirety for the duration of a single hop, from a forwarding node to an
o Network administrators SHOULD NOT accept prefixes when the first AS number in the AS path is not the one of the peer’s unless the peering is done toward a BGP
The required members in the input to the hash function are ordered lexicographically by the Unicode code points of the member names.. Characters in member names and member
When talking about users, we also need to distinguish the end user (who we typically think about when we talk about UI) from the server administrators and other technical