How TrustZone Could Be Bypassed: Side-Channel Attacks on a Modern System-on-Chip
Texte intégral
Figure


Documents relatifs
As a heuristic for this idea, suppose that, starting from a profile of sincere votes in the one-dimensional setting, voters who prefer the last- eliminated candidate, B, to the
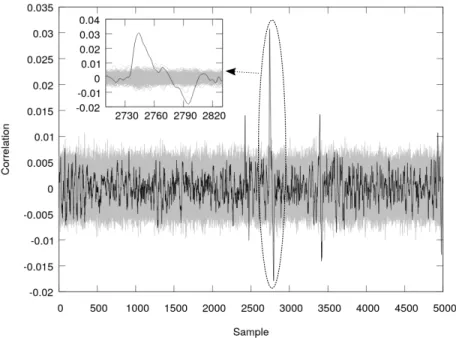
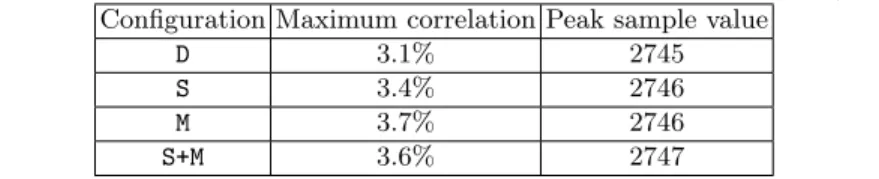
Taking a modern processor with a clock frequency of 3.2 GHz, and a Detection Module able to process 16 clock cycles of information at the same time, we can use a FPGA running at
In our case, we measure the optimality in terms of achieving the same success rate as the optimal strategy (using the exact ML distinguisher derived according to the knowledge of
In this work we propose the Gossip NoC, a security en- hanced architecture to deal with single and distributed timing attacks. It is composed by a traffic monitor and a counter-
To execute this meta-gadget, the attacker must craft a packet that, as a result of a buffer overflow, overwrites the return address with the address of gadget1, and injects into
/ La version de cette publication peut être l’une des suivantes : la version prépublication de l’auteur, la version acceptée du manuscrit ou la version de l’éditeur.. Access
Because CsA administration did not affect other factors known to modify IL-6 production during exercise (i.e., glycemia, running time, muscle glycogen content, and p38 MAPK response
In human colon cancer cell lines, the down regulation of LRH-1 by small interfering RNA leads to the reduction of steroidogenic enzyme expression and cortisol synthesis [18,