Gestion de la sécurité dans les systèmes de télécommunications : modèles, polyèdre et algorithmes
Texte intégral
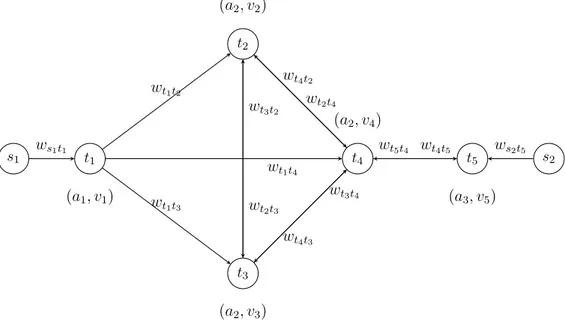
Figure


Documents relatifs
For numbers of points that are integer powers of a prime base, the construction of embedded rank-1 lattice rules is supported through any of these algorithms, and through a fast
Actually our method of proof gives a result of the type stated in the Theorem also under the assumption that the quotients α i /α u are not transcendental but have logarithmic
• c) find real points on every semi-algebraically connected component of a real algebraic set defined by a single equation, using the critical point method,.. • d) find real points
A bilingual Sub-regional Committee meeting costs at least five thousand US dollars in secretariat expenses, 4» It would therefore be both advantageous and practical to provide for
Motivated by applications in mathematical imaging, asymptotic expansions of the heat generated by single, or well separated, small particles are derived in [5, 7] based on
We show, in the limit of a one-dimensional flow computed by our two-dimensional solver, or for flows in a cylindrical geometry, that the scheme recovers the classical Godunov
To prove the Main Theorem we shall first prove a detailed characte- rization Theorem analogous to the covariant case ( see below).. Th e
PULTR, On categorical embeddings of topological structures into algebraic ones, Comment.. HEDRLIN, Extension of structures and full embeddings of categories, Actes