Techniques for a selective encryption of uncompressed and compressed images
Texte intégral
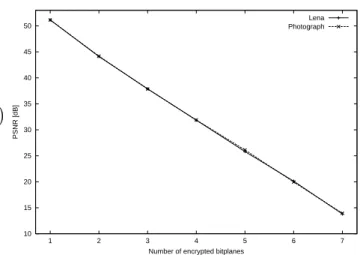
Figure



Documents relatifs
The image encryption schemes proposed by Zhou are implemented by digital encryption algorithms, such as discrete fractional Fourier transform (DFrFT), reality-preserving transform
For real-time implementation, we create the plaintext X i first by putting the indices of codewords from C2DVLC bit- stream, which is then encrypted to create Y i and then
This conjecture, which is similar in spirit to the Hodge conjecture, is one of the central conjectures about algebraic independence and transcendental numbers, and is related to many
Our second attack shows that when random nonces are used and when the length of the associated data is missing, 2 ℓ/2 encryption queries allows to forge a valid encrypted message
The key itself is encrypted prior to be used for plain text encryption and cipher text decryption processes, then it is hidden inside the cipher text.. The aim of hiding the key
To avoid the generation of larger f m 0 from the known f m , larger n 0 or the floating-point arithmetic is suggested being used to gen- erate {x(i)} M N/8−1 i=0. 5, we show
In addition, during the development of RC5, we began to focus our atten- tion on a intriguing new cryptographic primitive: data-dependent rotations , in which one word of
3.1 Average fraction of key space equation Firstly we need to determine the probability of the key of length n with exactly k ones on xedly chosen positions if in the
![Table 3: Execution times in [ms] (see [10]).](https://thumb-eu.123doks.com/thumbv2/123doknet/5936752.146141/6.918.87.440.732.983/table-execution-times-in-ms-see.webp)